ISO 27001
What is ISO 27001?
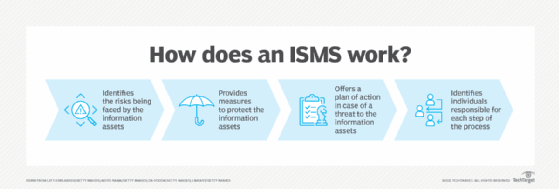
ISO 27001, formally known as ISO/IEC 27001:2022, is an information security standard created by the International Organization for Standardization (ISO), which provides a framework and guidelines for establishing, implementing and managing an information security management system (ISMS).
According to its documentation, ISO 27001 was developed to "provide a model for establishing, implementing, operating, monitoring, reviewing, maintaining and improving an information security management system."
The specification includes details for documentation, management responsibility, internal audits, continual improvement, and corrective and preventive action. The standard requires cooperation among all sections of an organization.
The goal of ISO 27001 is to help organizations protect their critical information assets and comply with applicable legal and regulatory requirements.
Organizations should apply the controls specified in ISO 27001 appropriately, in line with their specific risks. Third-party accredited certification is recommended for ISO 27001 conformance but not required as individual controls depend on the unique risks of each business.
Introduction to ISO 27001
ISO 27001 uses a top-down, risk-based approach and is technology-neutral. The specification defines a set of security controls that are divided into 14 sections, each containing specific requirements.
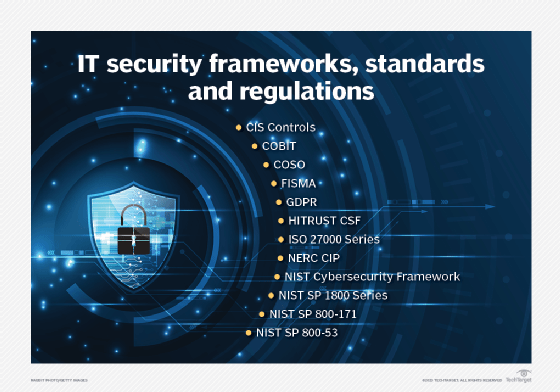
ISO 27001 also includes a set of control objectives and activities to help organizations reduce the risk of data breaches and other security incidents. Organizations may use ISO 27001 as part of their overall information security strategy, or they can choose to be certified by an ISO-accredited certification body.
ISO 27001 certification shows an organization's commitment to protecting their critical data assets and complying with applicable laws and regulations.
The 14 phases of ISO 27001
ISO 27001 is currently the most widely adopted international information security standard and is used by organizations all over the world. By following ISO 27001, organizations can be confident that their ISMSes are up to date and comply with current best practices.
To do so, ISO 27001 provides a comprehensive framework that helps organizations develop and maintain a secure ISMS. ISO 27001 is divided into 14 phases:
- Information Security Policy
- Organization of Information Security
- Risk Assessment and Treatment
- Asset Management
- Access Control
- Cryptography
- Physical Security
- Operations Security
- Communications Security
- System Acquisition, Development and Maintenance
- Supplier Relationships
- Compliance with Legal Requirements and Industry Standards
- Information Quality Management
- Risk Monitoring and Review
Best practices for preparing for ISO 27001 certification
ISO 27001 is a powerful tool for organizations to use when creating a secure ISMS, but it's important to remember that ISO 27001 is a framework, not an inflexible set of rules.
That means it must be studied, adapted and applied in the context of each organization's unique needs and circumstances. ISO 27001 provides best practices and guidance, but it's up to each organization to develop its own ISO 27001-compliant information security system.
Organizations should find an ISO-accredited certification body to assess their ISO 27001 compliance and provide training on topics such as risk assessment, access control, cryptography, physical security, communications security and more.
Organizations should also ensure they have the resources in place to plan and implement ISO 27001-compliant processes and controls.
Getting prepared for ISO 27001 certification
Using the steps below, organizations can ensure that they are properly prepared for ISO 27001 certification. Doing so helps protect their critical data assets and comply with applicable laws and regulations:
- Step 1. Build an ISO 27001-compliant ISMS.
- Step 2. Identify risks, and develop risk treatment strategies.
- Step 3. Implement ISO 27001-compliant processes and controls.
- Step 4. Have ISO-accredited certification body assess compliance.
- Step 5. Monitor your ISO 27001 compliance regularly.

By following ISO 27001, organizations can reduce the risk of data breaches and other security incidents, protect their critical information assets, and comply with applicable legal and regulatory requirements.
Other standards in the 27000 family
There are several other standards being developed in the 27000 family:
- ISO/IEC 27003 -- implementation guidance;
- ISO/IEC 27031 -- resilience;
- ISO/IEC 27005 -- risk management guidance;
- ISO/IEC 27032 -- cybersecurity guidance;
- ISO/IEC 27033 -- network security guidance;
- ISO/IEC 27034 -- application security guidance;
- ISO/IEC 27035 -- incident management guidance;
- ISO/IEC 27036 -- information exchange protection guidelines for cloud and other outsourced services; and
- ISO/IEC 27037 -- digital evidence handling guidelines.
Learn about the different types of cybersecurity controls and how to place them, and see how organizations can make educating their employees on cybersecurity risks interesting. Explore compliance and its related security concerns and nine common risk management failures and how to avoid them.
